Google's Web site malware checker identified TwitPic as a security threat today, a classification that has the popular photo...
Tag Archive for: Information Security
The Year in Cybersecurity: Malware, Social Media and Web Exploits
DT, , Information Security, Uncategorized, cybercriminals, cybersecurity, Facebook, Information Security, IT organizations, malicious code, Malware, malware attack, malware threats, Security Threat, social engineering attacks, social media, Trojan horse virus, Twitter, Web Exploits, 0This was the year of malware. In particular, according to the latest Sophos annnual report on cybersecurity, the year...
New Mac malware spreading from Dalai Lama tribute site
DT, , Information Security, Uncategorized, Dalai Lama, Information Security, Mac, Malware, New Mac malware, 0"Dockster" takes advantage of the same vulnerability exploited by the "Flashback" malware, which infected more than 600,000 computers.
Phishing Scams and Spam Reportedly Down in October
DT, , Information Security, Uncategorized, Hackers, Information Security, Internet security, Kaspersky Lab, Phishing, phishing attacks, scams, spam, 0Phishing scams on social networks have shrunk considerably in October, and spam in general has decreased too, according to...
Hootsuite flub reveals users’ e-mail addresses to other users
DT, , Information Security, Uncategorized, : e-mail, Hootsuite, Information Security, Privacy, Privacy and data protection, Seesmic, social faux, Social Media Management, Social media management company, Twitter, 0Social media management company Hootsuite has managed a social faux pas by sending e-mails to users that included the...
Anonymous hacking spree hits PayPal, Symantec
DT, , Information Security, Uncategorized, Anonymous hacking, hacking, Hacktivists, Information Security, Pastebin, PayPal, surveillance systems, Symantec, YouTube, 0The press arm for Anonymous has announced that it has begun its hacking spree for the 5th of November...
Cloud computing: Why it’s good for your bottom line
DT, , Cloud Computing, Uncategorized, Applications, Business leaders, Cloud Computing, cloud users, data, entrepreneurs, flexibilty, Information Security, IT infrastructure, Privacy, Reliability and continuity, resources, Small and medium-sized enterprises, SMEs, 0At its most basic, cloud computing is the shared use of the Internet to access data, applications, resources and...
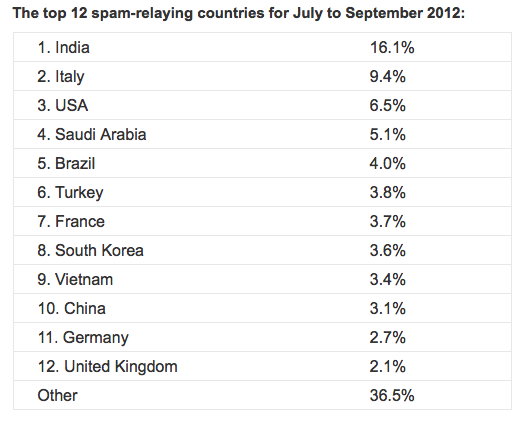
India is world leader in spam output
DT, , Technology, Uncategorized, botnets, cybercriminals, global spam, India, Information Security, IT security, malware infections, spam, spamming, Trojans, Viruses, Worms, 0A new report shows that computers based in India now send out more spam than ever before, with some...
FBI Warns of Malware Targeting Android Phones
DT, , Information Security, Uncategorized, Antivirus Software, attacks, data breach, FBI, Hackers, hidden security dangers, Information Security, Malware, malware protection, Malware Targeting Android Phones, private web developer, security dangers, security exploits, Security Risks, security weaknesses, Small businesses, spam, SQL injection attacks, web development, Web hosting, 0The FBI‘s Internet Crime Complaint Center is warning smartphone users of malware that targets Android operating systems. “Loozon” and “FinFisher”...
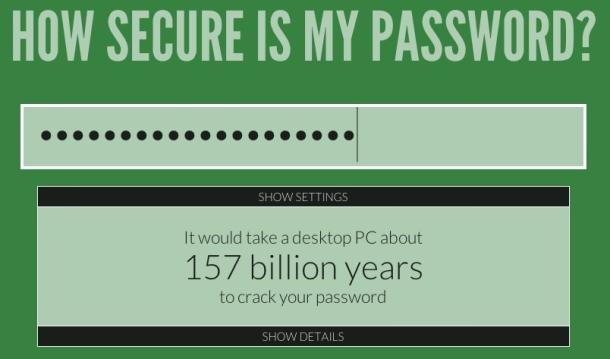
Ten simple, common-sense security tips
DT, , Information Security, Uncategorized, Backups, Bing, Google, ID theft, Information Security, Ixquick metasearch engine, passwords, Privacy, search engines, Security, security tips, VPN, 0A friend took me to task last week for a post I wrote back in January on preventing Google...