A friend took me to task last week for a post I wrote back in January on preventing Google...
Cloud Computing – The Social Evolution
DT, , Cloud Computing, Uncategorized, Applications, Cloud Computing, cloud security, computing devices, Ethernet infrastructure, Government, high powered computing, industry leaders, infrastructure, Internet, iPhone, IT industry, levels of government, Operating System, private, private industry, Public, public organizations, Security, Social Evolution, software application, working environment, 0Following the high-tech bubble burst at the start of this millennium, there have been very few advents in the...
Top 5 Cloud Computing Trends Of The Future
DT, , Cloud Computing, List, Applications, business processes, Cloud Computing, cloud computing issues, cloud computing migration elements, Cloud Computing Trends, cloud services, dynamic technology, hybrid cloud computing, infrastructure, investment value, iPhones, IT capacity, Security, security applications, smartphones, software, technology, traditional software, 0Cloud computing as a technology trend has caught up fast in recent years. It has revolutionized IT in a...
Cloud Computing Pushes Vendors to Seek New Roles in IT Value Chain
DT, , Cloud Computing, Uncategorized, Amazon, Amazon Web Services, automated computing capability, automation requirements, cloud adoption, Cloud Computing, cloud computing business, Cloud Computing Business Model, cost allocation, IT, IT organizations, job opportunities, SaaS, SaaS vendor, Security, Value Chain, Vendors, 0Cloud adoption means that companies are increasingly signing pay-as-you-go SLAs and renting servers. This means traditional software and hardware...
Cloud Computing Security – 10 Tips For Keeping Your Cloud Data Safe
DT, , Cloud Computing, Uncategorized, Cloud Computing, Cloud Computing Security, Cloud Data Safe, cloud data storage, cloud file-share and storage, cloud fileshare and storage, compliance, enterprise, enterprise storage, IT departments, Malware, Security, security and manageability, SkyDrive, software vendors, Tips, 0While we are all very happy about the entire cloud data storage concept and feel that it’s a breath...
Box beefs up security and search for enterprise storage
DT, , Cloud Computing, Uncategorized, Box security, Cloud Computing, cloud file-share and storage, cloud fileshare and storage, compliance, enterprise, enterprise storage, IT departments, Microsoft, Security, security and manageability, SkyDrive, software vendors, 0With more software vendors fielding their own cloud storage capabilities, Box continues to beef up enterprise security and perks...
Why IaaS Is The Easiest Phase Of Data Security In Cloud Computing
DT, , Cloud Computing, Information Security, PaaS, SaaS, Technology, backup programs, Cloud Computing, cloud computing environment, cloud data, computing environment, Data center, data centers, data facility, Data Security, Data Security In Cloud Computing, entrepreneur, IaaS, IaaS applications, IaaS environment, IaaS platform, Infrastructure as a Service, private network, private networks, safety measures, Security, security in cloud computing, Storage, storage equipment, the cloud, 0The cloud is expanding everyday and no longer looks like the shapeless puffy fleece that was until recently. The...
iPhone Software Glitch Puts Users at Risk for Scams
DT, , Information Security, Uncategorized, Apple, bogus messages, Information Security, iPhone, iPhone Software, Mobile, risk, scammers, scams, Security, 0The software that powers Apple's popular iPhones may have a flaw that enables scammers to send users bogus messages...
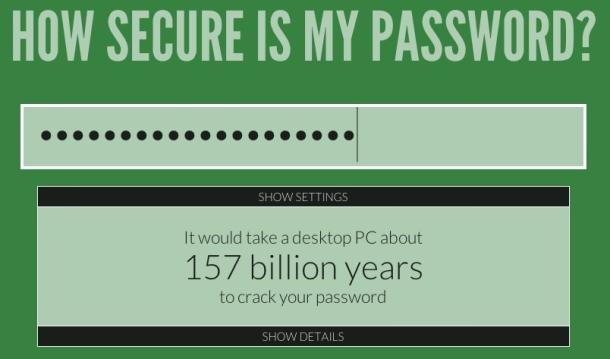
Facebook Privacy Chief: Never Surrender Your Password
DT, , Reports, Technology, Discrimination, Facebook, Facebook Password, Facebook Privacy, policies, Security, 0Facebook is mounting a strong resistance against the trend of employers and others forcing users of the social networks...