While BIM is frequently mistaken for just an enhanced form of CAD, its merits and virtues extend well beyond the ability to perform 3D modelling as it offers the additional bonus of advanced information and planning features.
One of the key advantages conferred by BIM usage is the ability of advanced information management to facilitate cooperation between the various stakeholders and contributors involved in a project. BIM is able to achieve this despite the disparate priorities and focus areas of the multiple parties required to bring a complex project to fruition.
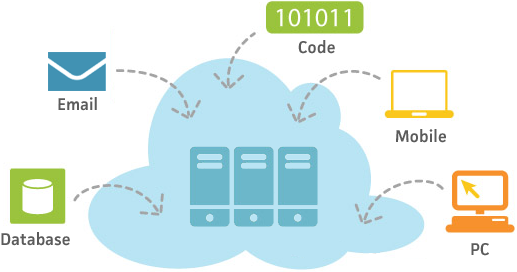
Cloud computing and BIM would appear upon first sight to be a perfect match. The use of the cloud – the provision of computing services to end users via virtual servers spread over a distributed system – promises to greatly augment BIM’s ability to facilitate cooperation by improving data sharing and software accessibility.
At its most basic, the storage of files and data in the cloud – which is equipped with virtually infinite memory space – makes it far easier for different parties to share and remotely access data despite belonging to different organizations or being situated in different geographic locations.
Different users can concurrently access large and complex BIM models sequestered in the cloud via multiple devices from virtually any location, by means of either software virtualisation programs which directly stream a user interface to client computers, or web-based applications akin to those currently provided by Google.
This provides major benefit to end users, dispensing with the need to install demanding IT packages on client computers, and increased flexibility of software access and updating.
In the wake of recent Internet spying revelations which have scandalized the international community, however, the question inevitably arises as to whether the incorporation of cloud computing poses a security risk to companies.
The idea that all the information and data required for a project – much of which is proprietary in nature and comprises vital assets for stakeholders – is situated in a diffuse virtual “cloud” of computing capability may be troubling to many. This is particularly true for those working in an industry whose basic materials are bricks and mortar and for whom drawings and blueprints on paper were until very recently the least tangible part of their trade.
Speaking at the sidelines of the Bentley Advantage Conference in Brisbane in November, Bhupinder Singh, senior vice president of Bentley Software, said any such concerns about the cloud security in relation to BIM usage are likely misplaced, since the technology can be deployed to varying extents depending on the specific needs of a project.
“Every company or government can look at at their own processes and ask themselves what aspects are better served through the cloud,” said Singh. “It isn’t a one size fits all, because some things may still need to be in-house.”
Different levels of usage and containment are available. Governments, for example, can make use of the cloud for certain processes, but also request that providers confine data storage to particular geographic regions. Companies can also adopt similar expedients, keeping data they consider vital and would prefer to remain exclusive on premises.
In the long term, however, Singh expects users to become more comfortable with cloud-based BIM usage as security and compliance measures evolve and users become accustomed to the concept of virtual servers.
“It will require a cultural and mindset change, as things are still evolving amongst providers of cloud services – such a standard levels of compliance and certification,” he said.
The cloud may also eventually prove to be a far safer option than conventional storage measures given the difference in security requirements for data centres and service providers as opposed to design, construction and engineering firms.
“To be honest with you from a data security standpoint, a remote data cloud environment in an exclusive facility can be far safer than an on-premises server in a company, where security measures may be laxer and people can come and go as they please,” Singh said.